The Danger of "Ghost" Users
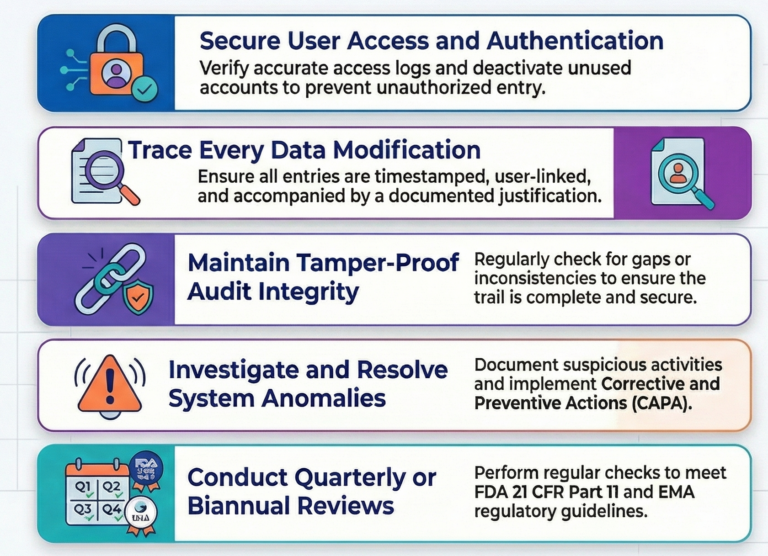
A secure audit trail is only as strong as the perimeter surrounding it. Regulatory standards demand that user access logs remain complete, accurate, and timely, supported by authentication processes that verify exactly who is entering the system. Administrative hygiene is the first line of defense, requiring teams to purge unused accounts and update access lists with clinical precision.
Overlooked, inactive accounts – frequently called “ghost users” – represent a massive liability. Even a system that meets every technical specification is compromised if an old account remains active, much like a high-tech bank vault left with the door slightly ajar. Deactivating these accounts isn’t just a technical task; it is a critical security mandate.
Beyond the "What" - The Mandatory "Why" of Data Changes
Traceability requires more than just recording a name and a date. Every data entry, modification, and system configuration change must be timestamped and linked to a specific user to ensure full accountability. Administrators must scrutinize system setting changes specifically, as unauthorized configuration shifts can compromise the integrity of the entire study.
The real power of the audit trail lies in the “justification” for every change. A timestamp tells you when a change occurred, but the justification provides the narrative that gives the data context. Without this documented “why,” a data point is stripped of its history, leaving it vulnerable to being viewed as unauthorized manipulation by regulators.
“By following a structured checklist and best practices, you ensure data integrity of your IRT and the system stays reliable and transparent.”
Hunting for Gaps - The Myth of the Perfect Audit Trail
We often assume that a “good” audit trail is one that is simply present and filled with data. However, true specialists know that the most dangerous threats are often found in the silence. High-level integrity requires a proactive search for what isn’t there, rather than just what is recorded.
Reviewers must actively hunt for gaps or inconsistencies, such as missing timestamps or sequences that skip unexpectedly. These anomalies are red flags that suggest data tampering or system failures. An audit trail is only truly secure when it is consistently scrutinized for these “missing pieces,” turning the log into a living witness of the trial’s accuracy.
Turning Anomalies into Evolution (CAPA)
When an investigation uncovers a suspicious activity or anomaly, it must lead to more than just a footnote. These findings should trigger formal Corrective and Preventive Actions (CAPA) to ensure the issue never repeats. This process of investigation and resolution must be fully documented to prove the system’s resilience.
Effective CAPA and continuous improvement are impossible without a properly trained workforce. By conducting reviews on a quarterly or biannual basis and ensuring everyone understands the “how” and “why” of the process, these findings evolve. They stop being simple error reports and become a blueprint for the continuous evolution of system security.
Navigating the Global Regulatory Maze
Navigating international standards like FDA 21 CFR Part 11 and EMA guidelines requires a shift in mindset. These regulations don’t just require a secure system; they require a secure process for monitoring that system. Every authorized configuration change and every finding must be recorded with meticulous care.
In the eyes of a global regulator, the mantra remains the same: if the review wasn’t documented, it never happened. Proving the process of security is just as important as the security itself. A robust audit trail review process ensures that when the inspectors arrive, the evidence of your oversight is ready and unassailable.
Conclusion: A Culture of Compliance
A structured IRT audit trail framework does more than check a box; it creates a culture of compliance that protects sponsors from the heavy hand of regulatory scrutiny. By transforming passive logs into an active oversight strategy, organizations move from reacting to the past to securing the future.
Is your audit trail a passive record of the past, or a proactive shield for your trial’s future?